Parenting Adult Children: The Consultant Protocol
Introduction: The Challenge of Parenting Adult Children
In the tech world, there is a clear distinction between a System Administrator and a Consultant. An Administrator has “Root Access”—they control the updates, manage the security, and decide which applications run and when. For twenty years, this was your role. You managed the “Hardware” (the home) and the “Software” (the education and values) of your children.
But when your children move out and become adults, your “Admin Access” is revoked.
The most common “System Crash” in the empty nest phase happens when parents try to use their old “Admin Password” to log into their adult child’s life. You try to tell them how to manage their finances, who to date, or how to run their household. When the “Command” is rejected, it leads to a Connection Timeout—silence, distance, and resentment.
To rank #1 on Google and solve this Reddit-level pain point, we must refactor your relationship. You are no longer the Administrator. You have been promoted to Senior Consultant.
-
Decommissioning the “Active Management” Module
The first step in the Consultant Protocol is acknowledging that the old “Management Module” is now “Legacy Code.” It served you well for two decades, but running it now creates “System Lag” in your child’s development.
The Problem with “Unsolicited Patches”
When you see your adult child making a mistake—perhaps they are overspending or choosing a sub-optimal career path—your instinct is to “Push a Patch” (give advice). In the Consultant Protocol, this is a violation of the User Agreement.
- The Error: Unsolicited advice is heard by an adult child as “I don’t think you are competent to run your own system.”
- The Fix: You must wait for a Service Request. A consultant only provides advice when the client asks for it. By holding back your “Patches,” you allow your child to build their own “Problem-Solving Logic.”
Parenting adult children effectively requires the discipline to watch them “Debug” their own lives. If you fix every bug for them, they never learn to secure their own architecture.
-
Refactoring Authority into Influence
In Phase 2.0, you are trading Power for Influence. Power is binary; it’s the ability to say “No” or “Do this.” Influence is analog; it’s the quiet respect you’ve earned that makes them want to hear your perspective.
The “Read-Only” Mode
Early in the transition, you must move your relationship into Read-Only Mode.
- Observation without Execution: You observe their choices, their successes, and their failures. You “Read” the data, but you do not “Execute” a change.
- Building Trustworthiness: By proving that you can listen without judging or interfering, you become a “Trusted Node” in their network. When a real “Critical System Failure” occurs, you will be the first person they call because they know you won’t try to seize control of their “Admin Console.”
-
The “Text Gap” and Latency Management
On Reddit, the #1 complaint from adult children is the “Text Bombing” from parents. This is a Bandwidth Issue. You have 100% “System Idle” time and want to fill it with “Pings” to your children. They are running “High-Load Processes” (new jobs, new relationships, independent lives) and cannot handle the frequency of your requests.

Calibrating the Communication API
To keep the connection healthy, you must optimize your communication for “Low Latency” and “High Value.”
- The 1:3 Ratio: For every three times they “Ping” you, you “Ping” them once. This ensures you are not “Flooding the Server.”
- The “Zero-Pressure” Ping: When you do reach out, ensure the message requires Zero Processing Power. Instead of asking “Why haven’t you called?” (which triggers a guilt-loop), send a “Low-Impact” message like: “Saw this and thought of you. No need to reply. Hope you’re having a great day!” This keeps the “Connection Heartbeat” alive without triggering the “System Overload” that causes adult children to “Ghost” their parents.
The “Bank of Mom and Dad” Firewall
Many empty nesters continue to provide “Subsidies” (paying for phone bills, car insurance, or rent). While this feels helpful, it can create a Dependency Loop that prevents the child from fully “Booting Up” their own financial independence.
- The Protocol: Define the “Sandbox” limits. If you are providing financial support, it should be for “System Upgrades” (education or a house down-payment) rather than “Operational Expenses” (daily lifestyle).
- The Sunset Clause: If you are currently paying for their “Subscriptions,” set a “Decommissioning Date.” This gives them a timeline to integrate these costs into their own budget.
-
Identifying “Enmeshment” Bugs
The final piece of Part 1 is identifying the “Enmeshment Bug.” This occurs when the parent’s “Emotional State” is “Tightly Coupled” with the child’s. If the child is sad, the parent crashes. If the child is successful, the parent feels validated.
Decoupling the Systems
Parenting adult children successfully means becoming “Loosely Coupled” systems.
- Independent Stability: Your “Happiness OS” should not be dependent on their “Status Reports.” You must have your own “Projects” (like this blog!) and your own “Social Nodes.”
- The Objective: When you are emotionally stable on your own, you become a “High-Availability Server.” You can provide support to them without being “Drained” by their volatility.
Third-Party Integrations and Conditional Advice Logic
-
The Third-Party Integration: Mastering the “Partner” API
One of the most frequent “System Failures” discussed on Reddit occurs when an adult child brings a partner into the family “Network.” Many parents view the new spouse or partner as an “Add-on” or a “Plugin” that should conform to the family’s existing “Standard Operating Procedures.”
In the Consultant Protocol, we treat the partner as a Third-Party Integration. They come with their own “Legacy Code” (upbringing), their own “Security Protocols” (boundaries), and their own “UI” (personality).
Avoiding the “In-Law” Compatibility Error
The “In-Law” conflict is essentially a Merge Conflict. Two different sets of family logic are trying to overwrite the same file (your child’s life).
- The Integration Rule: You cannot “Refactor” the partner. Any attempt to change them or criticize their “Code” will result in your child’s system “Firewalling” you.
- The Documentation Strategy: Your job is to learn their “API.” Observe how they communicate. Respect their “Private Partitions.” By treating the partner as an equal “System Admin” in your child’s life, you ensure your “Access Token” remains valid for the whole family.
-
The Advice Filter for Parenting Adult Children
As a Senior Consultant, your “Database” is full of valuable experience. You’ve already lived through the “System Crashes” your children are currently facing. However, the most effective consultants know that Data Transfer is only successful when the “Client” is ready to receive it.
- The Request for Data: If they don’t ask, they won’t “Process” what you say. It becomes “Background Noise” or, worse, “Spam.”
- The “I’m Curious” Loop: If you see a major error, instead of pushing advice, ask a “Discovery Question.” Example: “I see you’re looking at a new car. What’s your current logic for the budget?” This allows them to explain their “Architecture” without feeling attacked.
-
Handling “System Errors”: The Art of No-Blame Debugging
Adult children will inevitably experience “Hard Drive Failures”—divorce, job loss, or financial setbacks. In these moments, the temptation to say “I told you so” is a Critical Logic Error.
The “Disaster Recovery” Protocol
When your child’s life is in “Safe Mode,” they don’t need a critic; they need a Redundant Server.
- Zero-Blame Debugging: Focus on the “Current State,” not the “Input Error.” Don’t dwell on why it happened; focus on the “Path to Recovery.”
- The Support Buffer: Provide the “Bandwidth” they need to recover. This might mean temporary “Resource Allocation” (as we discussed in the Financial Sandbox in Post #7), but only as a “Hotfix” to get them back on their feet.
- Internal Link: Remember, any financial support should follow the strict logic of your [Financial Sandbox Rules], ensuring that your “Backup” doesn’t become their “Permanent Power Supply.”
-
The Holiday Protocol: Managing Shared Bandwidth
In the parenting years, holidays were “Hard-Coded.” Everyone was in the same house at the same time. In Phase 2.0, time becomes a Shared Resource that must be negotiated across multiple “Nodes” (your house, the in-laws’ house, their own home).
Resolving “Schedule Latency”
- Flexible Scheduling: Don’t insist on “Synchronous Communication” (everyone together on exactly the 25th). Be willing to move your “Holiday Event” to a different date to reduce the “Processing Load” on your children.
- The “Open-Source” Invitation: Let them know they are always welcome, but provide an “Opt-Out” clause. This prevents them from feeling like your “Client Node” is a burden. Paradoxically, the less you demand their time, the more they will likely “Commit” to spending it with you.
-
The “Ghosting” Bug: Handling Communication Latency
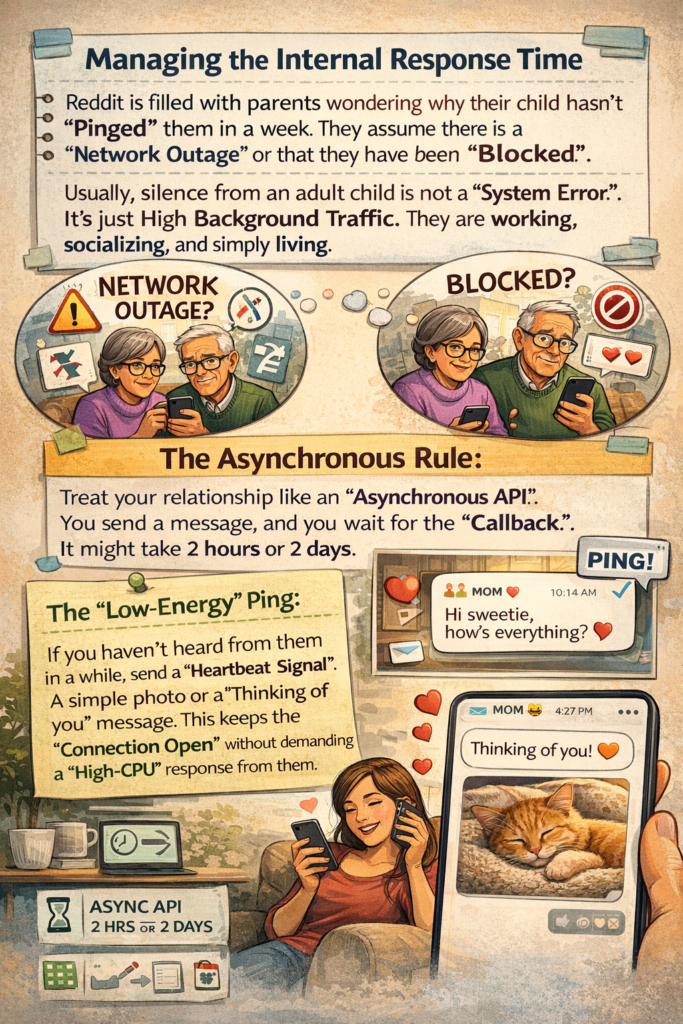
Reddit is filled with parents wondering why their child hasn’t “Pinged” them in a week. They assume there is a “Network Outage” or that they have been “Blocked.”
Managing the “Internal Response Time”
Usually, silence from an adult child is not a “System Error.” It’s just High Background Traffic. They are working, socialising, and simply living.
- The Asynchronous Rule: Treat your relationship like an “Asynchronous API.” You send a message, and you wait for the “Callback.” It might take 2 hours or 2 days.
- The “Low-Energy” Ping: If you haven’t heard from them in a while, send a “Heartbeat Signal.” A simple photo or a “Thinking of you” message. This keeps the “Connection Open” without demanding a “High-CPU” response from them.
-
Refactoring Your Expectations: Deleting the “Mini-Me” Script
One of the hardest “System Updates” for a parent is realizing that their child is not a Mirror Image of their own code. They may choose a religion, a political path, or a lifestyle that is “Incompatible” with your “Default Settings.”
Accepting “Alternative Operating Systems”
Parenting adult children is about respecting their “Kernel.” Even if you wouldn’t run their OS, you must respect that it is their machine.
- The Validation Script: Validate their “Logic,” even if you disagree with the “Output.” Saying, “I see why you made that choice, it fits your goals,” is a powerful way to stay “Logged In” to their life.
- The Sovereignty Protocol: Your child’s life is their “Private Server.” You are a “Guest User” with high-level privileges, but you do not have “Write Access.”
Legacy Plugins, Boomerang Loops, and Emotional Firewalls
-
The Grandparenting API: Deploying the “Legacy Plugin” for parenting adult children,
When your adult child has their own child, the relationship architecture undergoes another massive “System Migration.” You are no longer just a “Senior Consultant” to your child; you have become a Legacy Plugin for the next generation.
The “Grandparenting API” is a privileged but highly restricted access level. The most common error here is the Parental Override. You feel that because you raised children successfully, you have the “Master Code” for how your grandchildren should be raised.
Respecting the “New Project Manager”
In the Consultant Protocol, your child is now the Project Manager of their own family. You are a Sub-Contractor.
- The Permission Protocol: You do not feed, discipline, or schedule the grandchild without a “Authorized Request” from your adult child. If they say “No Sugar,” and you provide “Sugar.exe,” you are violating the security protocols of their household.
- The Consequences of “Shadow Code”: If you constantly override their parenting decisions, they will Revoke Your Token. This results in limited visits and “Connection Latency.” To stay “Logged In” to your grandchildren’s lives, you must respect the “Kernel Rules” set by your adult children.
-
The Boomerang Script: Living with and Parenting Adult Children Again
A “Boomerang Child” is an adult child who has “Failed to Launch” or has returned to the “Home Server” due to a job loss, divorce, or financial “System Crash.” While your instinct is to provide “Unlimited Hosting,” this can lead to a Dependency Loop that prevents the child from ever becoming an “Independent Node.”
Setting the “Terms of Service” (TOS)
If an adult child moves back home, you must not revert to “Version 2.0” (treating them like a teenager). You need a Service Level Agreement (SLA).
- Rent and Resource Allocation: Even if it’s a nominal amount, they should contribute to the “Operating Costs” of the household. This prevents them from becoming “Bloatware” and keeps their “Financial Logic” sharp.
- The Sunset Clause: Define a “Decommissioning Date.” Is this a 3-month “System Reset” or a 12-month “Rebuild”? Having a clear end-date prevents the stay from becoming a “Permanent Redirect.”
- Household Contributions: They are a co-habitant, not a guest. They should handle their own “Maintenance Scripts” (laundry, dishes, cooking) to maintain the dignity of their adult status.
-
The Emotional Firewall: Preventing “System Mirroring”
One of the most difficult parts of parenting adult children is watching them suffer. If your adult child is going through a “Critical System Failure”—like a bankruptcy or a painful breakup—your natural tendency is to Mirror their State. If they are miserable, you are miserable.
In computing, this is a Coupling Error. If the “Client” crashes, the “Server” (you) should remain stable to provide recovery options. If you crash too, the entire “Network” is down.
Building the “Identity Partition”
You must implement an Emotional Firewall to protect your own “System Integrity.”
- Empathy vs. Absorption: Empathy is “Read-Only Access”—you understand their pain. Absorption is “Full Write Access”—you take their pain into your own system.
- The “Not My Bug” Realization: You must accept that their “Software Bugs” (life choices and consequences) are not yours to fix. You can offer “Consultation,” but you cannot run the “Debug Script” for them.
- Maintaining Your Own Uptime: This is why your 20-Year Roadmap and your Health Architecture are so important. If you are healthy and focused on your own “Projects,” you have the “Processing Power” to be a supportive consultant without being destroyed by their volatility.
-
The “Guilt.exe” Malware: Deleting Parental Shame
Many parents of adult children suffer from a recurring background process: Parental Guilt. You look at your child’s struggles and think, “If only I had coded Version 2.0 better, they wouldn’t have this bug today.” This is “Legacy Malware.” It consumes massive “Mental RAM” and provides zero “Output.”
The “Final Build” Philosophy
- Accepting the Version History: You did the best you could with the “Tools” and “Knowledge” you had at the time. There is no such thing as “Perfect Code.”
- The Sovereignty Update: Once a child becomes an adult, they are responsible for their own “Updates.” They can choose to “Patch” the flaws they inherited from their upbringing. If they choose to stay “Unpatched” and blame you, that is their “Logic Error,” not yours.
- The Delete Command: Intentionally delete the guilt. It prevents you from being a good “Consultant” because it makes you defensive and over-apologetic. A good consultant is objective and focused on the future, not the “Legacy Bugs” of the past.
-
The “Advice on Demand” Infrastructure
How do you position yourself so that your children actually want to call you for advice? Most parents “Push” advice so hard that the children “Block” the signal. To rank #1 on Google, we must teach the readers how to become a High-Demand Consultant.
Becoming a “Pull” Resource
- The “Zero-Judgment” Buffer: If your child tells you about a mistake and your first response is a “System Warning” (criticism), they will stop sending you “Data Logs.” If your response is, “That sounds tough, how are you planning to handle it?” you remain a trusted node.
- The “Wisdom Portfolio”: Show, don’t just tell. When they see you managing your own Financial Sandbox successfully or staying healthy through your Physical Architecture, they will naturally “Query” you for your methods.
- The Power of “I Don’t Know”: A “Senior Consultant” isn’t afraid to say they don’t have the answer. If you try to “Brute Force” an answer to a problem you don’t understand (like their modern career in digital marketing), you lose “Credibility.” Admitting you don’t know makes your actual advice much more “Authoritative.”
-
Conflict Resolution: The Negotiation Protocol
In the parenting years, conflicts were resolved by “Admin Decree.” You had the power to “Kill the Process.” In parenting adult children, conflicts must be resolved through Negotiation.
The “Win-Win” Merge
When a “Merge Conflict” occurs (e.g., they want to skip a family wedding you think is important):
- State the “Business Requirement”: “It’s important to me that our family shows a united front at this event.”
- Listen to their “Constraint”: “I understand you have a high-load project at work and the travel time is too much.”
- Find the “Workaround”: “Could you attend just the ceremony and fly back the same evening? Or could we do a video-call ‘Virtual Appearance’ during the toast?”
By treating conflict as a “Technical Problem” to be solved rather than a “Disrespect Issue,” you keep the “Emotional Latency” low and the “Relationship Uptime” high.
Values, Legacy, and the Data Migration Protocol
-
Passing the “Source Code”: Sharing Values Without Force-Installing
One of the deepest fears in parenting adult children is that they will “Delete” the values they were raised with. You spent years “Hard-Coding” honesty, hard work, and kindness into their “Version 1.0.” Now that they are independent nodes, parenting adult children often involves watching them make choices that look like “Bad Code”—perhaps different political views, religious shifts, or lifestyle changes that challenge your original programming.
Inspirational Documentation vs. Mandatory Scripts
In the Consultant Protocol of parenting adult children, you must realize that you cannot Force-Install your values anymore. If you try to push a mandatory script, the “Internal Firewall” of the adult child will mark your advice as “Malware” and block the connection entirely.
-
The Open-Source Model: When parenting adult children, treat your values as “Open-Source Code.” You put the documentation out there—you live your life with integrity, you show the results of your hard work—and you let them “Fork” the code. They might take the parts they like and modify the rest to fit their own “Operating System.”
-
Leading by Output, Not Input: A successful strategy for parenting adult children is focusing on output. Don’t tell them why they should be frugal; show them the “Stability” of your Financial Sandbox. When they see that your “System” works, they will naturally look at your “Source Code” for inspiration.
-
The “Legacy Repository”: Use a “Legacy Repository” to share stories of why you believe what you believe. This is a powerful technique for parenting adult children because it uses “Narrative Data” rather than “Moral Commands.” Stories bypass the ego’s firewall and get stored in their long-term “Memory Cache.”
-
The Inheritance Dialogue: Decrypting the Financial Roadmap
Money is the most “Encrypted” topic in family systems. Many parents keep their wealth “Hidden in a Private Partition,” fearing that if their children know the “Balance,” they will lose their “Motivation Logic.” However, a lack of transparency often leads to “System Corruption” later on, such as confusion during an estate handover or resentment over perceived “Resource Hoarding.”
The “Transparent Data Migration” Strategy
Parenting adult children involves preparing them for the eventual “Data Migration” of your assets.
- The Level 1 Disclosure: You don’t need to show them the full “Database” yet. Start by discussing the “Architecture.” Tell them you have a plan, where the “Encryption Keys” (Wills and Trust documents) are stored, and who the “Backup Admin” (Executor) is.
- Teaching Financial Logic: Instead of just giving them “Files” (money), give them the “Algorithm.” Discuss how you manage risk and inflation. This ensures that when the “Full Migration” eventually happens, they have the “Software” needed to run the “Hardware” (wealth) you’ve built.
- Internal Link: This section ties directly into our [Generational Wealth for Empty Nesters] guide (Post #10). Ensuring your children are “Beta-Tested” in financial literacy is the best way to protect your legacy.
-
The “Generational Handover”: Promoting the Child to “Lead Developer”
There comes a point in the lifecycle where the “Primary Node” of the family begins to shift. For years, you were the center of the family “Network.” You hosted the holidays, made the big decisions, and provided the “Core Stability.”
Stepping Back to “Senior Consultant”
Part of the Consultant Protocol is knowing when to let your adult child take the “Lead Developer” role for family events or decisions.
- The “Holiday Migration”: If your adult child wants to host the family dinner, let them. Even if their “Execution” isn’t as polished as yours, do not “Micro-manage the Process.” Be the “Support Staff.”
- The “Succession Plan”: Gradually involve them in the “Admin Tasks” of the extended family—managing the care of aging grandparents or planning family reunions. This builds their “Leadership Capacity” while you are still around to provide “Consultative Backup.”
- The Benefit: By promoting them to “Lead,” you ensure the family “System” remains functional even when you decide to go “Offline” for extended travels or personal projects.
-
Building the Family “Wiki”: The Shared Knowledge Base
In high-performance organizations, knowledge isn’t stored in one person’s head; it’s in a Shared Wiki. In a family, this includes the “Unwritten Rules,” the “Family Recipes,” and the “Success Stories.”
The Documentation Layer of the Consultant Protocol
The Digital Repository: When parenting adult children, use tools like Google Drive, Notion, or a shared Family App to store “Metadata.” This digital hub is a core component of parenting adult children, housing folders of scanned old photos, documents like “Advice for the Grandkids,” or a “Troubleshooting Guide” for the family business.
The Story-Harvesting Protocol: Once a year, perform a “Data Dump” as part of your long-term strategy for parenting adult children. Record a video or write a post about a specific challenge you overcame. This becomes the “Legacy Database” that your children and grandchildren can “Query” for generations to come, ensuring your “Source Code” is never lost.
The Connection ROI: Working on a “Shared Project” like a family history book or a digital archive is a powerful way to “Sync” with your children. It provides a neutral, high-value environment for parenting adult children without the friction or pressure of “Direct Parenting.”
-
Handling the “Aging Parent” Paradox: The Flipped API
As you move into Phase 2.0, you may find your “Hardware” beginning to show signs of “Age-Related Latency.” This creates a paradox: you are trying to be a Consultant to your adult children, but they are beginning to feel the need to become Administrators for you.
Managing the “System Reversal”
This is the most sensitive part of parenting adult children. They may start “Hovering” over your health or finances.
- The Independence Firewall: Maintain your “System Autonomy” for as long as possible by following the [Health Architecture] we built in Post #11. The better you maintain your “Hardware,” the longer you remain the Consultant.
- The “Authorized Access” List: Be proactive. Tell them: “I am the Admin of my life right now. But if my ‘Core System’ ever goes into ‘Safe Mode’ (health crisis), here is the protocol I want you to follow.” * The Logic: By providing them with a “Pre-defined Response Script,” you prevent them from having to make “High-Stress Decisions” on your behalf. This keeps the relationship focused on “Connection” rather than “Crisis Management.”
-
Deleting the “Expectation.exe” Malware
The final “Bug” in the legacy phase is the weight of Unspoken Expectations. You expect them to call on Sundays; they expect you to babysit every Friday. When these expectations aren’t “Documented,” they lead to “System Crashes.”
The “Explicit Request” Protocol
- Clear Input/Output: Instead of feeling hurt that they didn’t visit, send a “Service Request”: “I would love to have a 1-hour ‘Sync’ with you this weekend. Does Saturday at 10 AM fit your ‘Schedule Throughput’?” * The “Zero-Obligation” Clause: Always give them an “Out.” This ensures that when they do say yes, it’s a “Genuine Connection” rather than a “Forced Process.”
- The ROI: Explicit communication reduces the “Background Noise” of resentment. It keeps the “Link Quality” high and the “Latency” low.
System Maintenance, Error Handling, and the Final Deployment
-
The Daily Maintenance Log for Parenting Adult Children
In high-performance computing, the difference between a stable system and one that crashes is Routine Maintenance. You don’t wait for a “Critical Error” to check the logs. Similarly, parenting adult children requires small, daily habits that keep the “Connection Heartbeat” strong without consuming too much “Resource Bandwidth.”
The “Low-Latency” Daily Script
- The “Zero-Pressure” Ping: Once or twice a week, send a “Status-Neutral” message. This could be a link to an article they’d like, a photo of the family dog, or a simple “Thinking of you.” This tells their system that your “Server” is online and friendly, without requiring them to “Process” a long reply.
- The “Self-Optimization” Window: Spend at least two hours a day on your own “Projects”—like your blog or your [Health Architecture]. When you are busy with your own “Code,” you are less likely to “Hover” over theirs.
- Active Listening Mode: When they do call, toggle your “Input/Output” settings. Aim for a 70/30 Listen-to-Talk ratio. Your goal is to be a “Data Sink”—letting them dump their stress and thoughts without you immediately trying to “Refactor” their story.
-
Critical Error Handling: Resolving “System Outages” when Parenting Adult Children
Sometimes, despite your best efforts, the relationship experiences a System Outage (estrangement or long-term silence). This is the most painful “Bug” in parenting adult children. On Reddit, parents often panic and try to “Brute Force” the connection by calling repeatedly or showing up unannounced. This almost always leads to a “Permanent Block.”
The “Re-Boot” Protocol for Broken Connections
- Stop the “Retry” Loop: If they have stopped responding, stop “Pinging.” Constant attempts to connect during an outage act like a DDoS Attack on their emotional system. It causes them to “Shut Down” even further.
- The “Apology Patch”: If the outage was caused by your “Admin Overreach” (criticizing their life or partner), send a single, high-quality “Patch.” Do not explain why you did it. Simply say: “I realize I overstepped my boundaries. I am sorry for the stress I caused. I am here whenever you are ready to reconnect.”
- The “Background Processing” Phase: While the connection is offline, work on your own “Internal Logic.” Focus on why you felt the need to control. By the time the “Handshake” happens again, you should be a “V3.0” version of yourself—more stable and less reactive.
Conclusion: The Final Deployment in Parenting Adult Children
You have now completed the most comprehensive guide to parenting adult children available on the web. We have refactored the relationship from one of “Control” to one of “Consultancy.”
By following the Consultant Protocol, you are doing more than just avoiding “Merge Conflicts.” You are building a “High-Integrity Network” that can last for the rest of your life. You are moving from a state of “Hyper-Vigilance” to a state of Strategic Influence.
- The Admin Password has been handed over.
- The Consultant API is open.
- The System is Stable.
It is time to Log In to your new life.

